Hashing Algorithms And Security Computerphile Hashing Algorithms And Security Computerphile
Net Worth Profile Overview
Hashing Algorithms And Security Computerphile Hashing Algorithms And Security Computerphile Net Worth & Biography

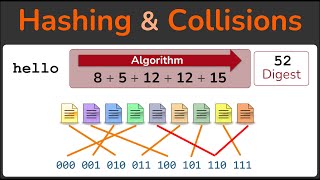
Learn more about the Jane Street internship at SHA2's weakness explained by Dr Mike Pound -- Check out Brilliant's courses and start for free at ... If you pick the wrong prime numbers, cracking RSA becomes a cinch. Dr Mike Pound explains the findings of researcher Hanno ... Featuring Mike Pound. Jane Street skyscraper puzzle (and info on the AMP program) at Spies used to meet in the park to exchange code words, now things have moved on - Robert Miles explains the principle of ... Wanacrypt works super fast and even when you're offline. Dr Pound explains how hybrid ransomware systems work. Original ...
Connecting via SSH to a remote machine is second nature to some, but how does it work? Dr Steve Bagley. Dr Mike Pound on ... One of the most elegant solutions for cryptography. Dr Mike Pound explains one of his most favourite ciphers.
Estimated Worth: $10M - $34M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: May 15, 2026
Net Worth Outlook & Future Earnings

Disclaimer: Disclaimer: Net Worth estimates are based on publicly available data, media reports, and financial analysis. Actual numbers may vary.